As a beginner in Linux, you may have noticed that some files and directories in your file system are not visible when using the standard “ls” command. These files and directories are known as hidden files and are prefixed with a dot (.) character. In this guide, we will take a closer look at hidden files in Linux and how to manipulate them.
First, it’s important to understand that hidden files are not a special type of file in Linux. They are simply regular files and directories that have been given a special name to make them hidden. The dot (.) prefix is used as a convention to indicate that the file or directory should be hidden.
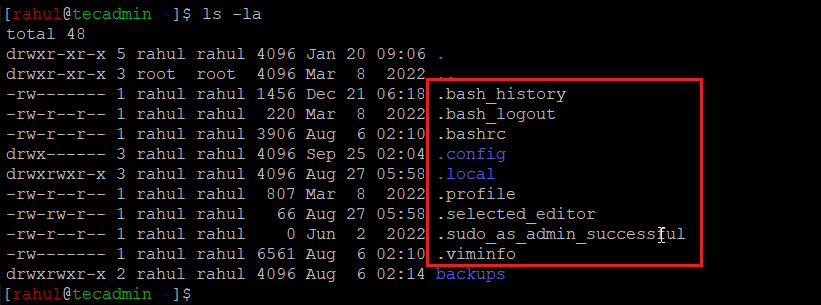
Listing the hidden files in Linux
The hidden file is used to hide specific files and directories in the current directory. When a file or directory names start with dot (.) character, it will not be displayed when using the “ls” command. You can use “-a” comamnd line option with ‘ls’ command to display hidden file also.
ls -a
You can also use ‘ls -la’ for long listing of files including hidden files.
Creating a hidden file in Linux
To create a hidden file, the user can simply create a new file name starting with (.) character. Any file or directory name started with a dot (.) character are consider as hidden files.
For example, to create a hidden file named “.htaccess”, execute:
touch .htaccess
Is hidden files are Secure?
One important thing to keep in mind is that the hidden file is not a security feature. It is just a way to hide files from a standard file listing, and it does not prevent the files from being accessed by other means. The files can still be accessed by their full path name or by using the “-a” option with the “ls” command. Therefore, it is not recommended to rely on the hidden file to protect sensitive information, and it should be used only to make the file system easier to navigate.
Wrap Up
In conclusion, a hidden file is a useful tool for hiding specific files and directories in the Linux file system. It can be used to declutter the file listing and make it easier to find the files the user is looking for. However, it should not be considered as a security feature and should not be used to protect sensitive information. Users should use other means such as access controls and encryption to protect sensitive information.
