Let’s Encrypt is Certificate Authority (CA), which provides free SSL certificates for your domains to secure data on the transport layer. This tutorial will help you to install and secure Apache with a free SSL certificate issued by Let’s encrypt.
Prerequisites
- Running CentOS 8 machine with shell access
- Follow initial server setup steps for newly installed machine
- A domain/sub domain pointed to server IP address via public DNS server. For this tutorial, we use webhost.tecadmin.net.
Step 1 – Install Apache
First of all, Install the Apache server on your CentOS 8 machine. The Apache packages are available under the default repositories.
sudo dnf install httpd httpd-tools mod_ssl
Step 2 – Create VirtualHost with Port 80
For this tutorial, I have created a index.html file under the default document root. Similarly, you can place your application under the document root of your domain.
sudo echo "<h2>Welcome to Secure TecAdmin.net</h2>" > /var/www/html/index.html
After that, create a VirtualHost configuration file binding with port 80.
sudo vim /etc/httpd/conf.d/webhost.tecadmin.net.conf
1 2 3 4 5 | <VirtualHost *:80> ServerAdmin admin@example.com ServerName webhost.tecadmin.net DocumentRoot /var/www/html </VirtualHost> |
Save and close the file. Restart Apache service to reload the configuration.
sudo systemctl restart httpd.service
Step 3 – Setup Let’s Encrypt (Certbot) Client
The Certbot ACME is a client application recommended by the Let’s Encrypt for systems with shell access. It provides hassle-free automation of the certificate issuance, installation, and renewal.
You can download the certbot-auto script from the official download page and put it under /usr/sbin directory. Use the following command to do it.
sudo wget https://dl.eff.org/certbot-auto -O /usr/sbin/certbot-auto sudo chmod a+x /usr/sbin/certbot-auto
You also need to installed all dependency for the certbot to make it work. The below command will install it dependencies on your system.
sudo certbot-auto --os-packages-only
Step 4 – Create Let’s Encrypt Certificate
Now, you can request Lets encrypt to issue a SSL certificate for you domain. You need to run the certbot-auto command for Apache server as following:
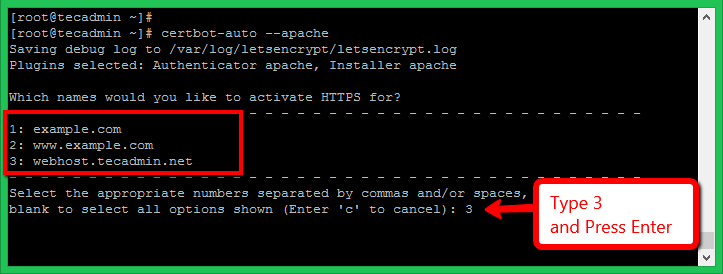
sudo certbot-auto --apache
This will list all the virtual hosts configured with Apache on current server. Select the appropriate number with the comma separated. See below screenshot:
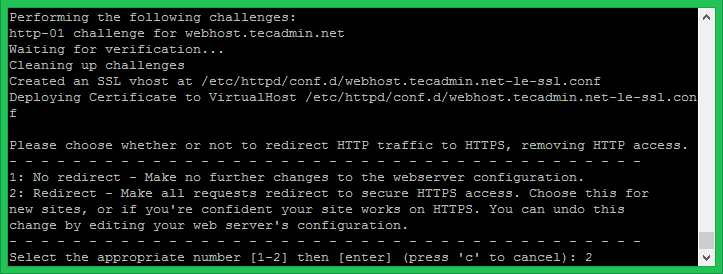
The Let’s encrypt will start the verification process for your domain. Make sure the domain you selected is pointed to this server via the public DNS server.
On successful verification, SSL will be issued for your domain. A separate SSL VirtualHost configuration file will be created for your domain.
Please choose whether or not to redirect HTTP traffic to HTTPS:
- 1: No redirect – Make no further changes to the webserver configuration.
- 2: Redirect – Make all requests redirect to secure HTTPS access.
Enter a number of your choice and press enter. You can also change it latest by directly editing configuration files.
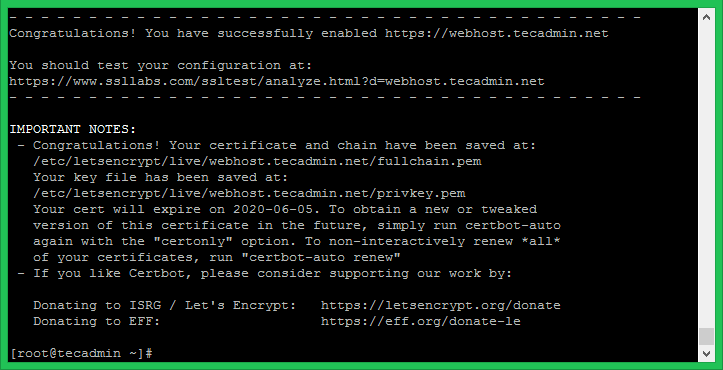
Once the SSL configuration completed successfully, you will see a congratulations message on your screen.
Step 5 – Verify Certificate
The Let’s Encrypt SSL has been successfully configured for your domain. This certificate is issued for 3 months only, You can renew it before expiration.
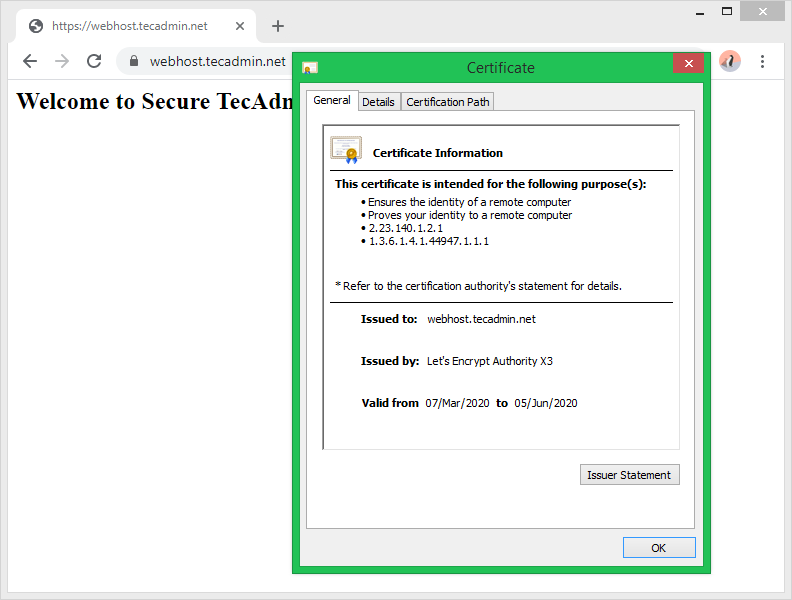
Let’s check the certificate by accessing your site in a web browser.
Conclusion
You have successfully secured your website with free Let’s Encrypt SSL certificate. Follow our next tutorial to setup Let’s Encrypt Auto SSL renewal with crontab. The CentOS 8 systems will have default TLS 1.2 and TLS 1.3 enabled.

3 Comments
To make things less painful, use Cloudflare free plans and have SSL that works everywhere. Also set up automatic rewrites to https in Cloudflate, remove your web server https redirect (if any), close port 80, and encrypt all the things!
You should clarify that this does not work on local network servers. I wasted several hours trying to figure this out only to find it is impossible.
Hi Rahul, on a fresh install of RHEL 8.2 (AWS image) when running certbot-auto I get the error
Error while running apachectl configtest.
AH00526: Syntax error on line 85 of /etc/httpd/conf.d/ssl.conf:
SSLCertificateFile: file ‘/etc/pki/tls/certs/localhost.crt’ does not exist or is empty
because when mod_ssl package is installed, it doesn’t create a self-signed key and certificate files for the localhost, like it should. To solve the error, run:
/usr/libexec/httpd-ssl-gencerts
(Found the solution here: https://github.com/certbot/certbot/issues/7397)