Accessing computers remotely has become an important part of the IT world especially in today’s scenario where everyone is working from home due to covid19. There are mainly two ways of connecting machines remotely depending on your operating system:
- SSH for Linux
- RDP for Windows
In this tutorial, we will see how to use SSH to connect to a remote server?
What is SSH?
SSH stands for Secure Socket Shell and it is a network protocol used to access a system remotely in a secured way. SSH is an application layer protocol and it allows you to access another machine without physical access. Simply, you can control the servers remotely via the internet.
In the early 90s, IT professionals were using Telnet for data transfer. It was an application layer protocol and used to transfer data without encryption. Later SSH was created as a secured alternative to Telnet which encrypts data so that others cannot retrieve it without access.
SSH allows encrypted communication between two computers and also, it is used to manage systems and applications remotely. With the help of SSH you can:
- Issue remote commands
- Transfer files, data, text
- Connect to remote servers
- Provide secure access for automated processes and users.
How does SSH work?
It works by connecting a client device with an SSH server. You can start the server on Ubuntu by running sudo systemctl start ssh. You install the SSh application on the client-side and provide information related to the remote server. On the server-side, There will be an SSH daemon that continuously checks for specific TCP/IP ports for client connection requests. Once the client initiates the connection requests with the right credentials, the SSH daemon starts exchanging the identification data with the client to establish a secured remote connection.
So to connect to a remote server using SSH, you need to make sure that SSH is installed on both the server and client devices. In this tutorial, we will use OpenSSH which is an open-source SSH tool for Linux. First, we will install it on both the client and remote devices and then we will use it to connect to the remote device.
Installing an OpenSSH server
The server machine which you are trying to access with SSH must have a server-side part of the SSH software kit. You can also check if you have already installed the OpenSSH server on the remote server or not by connecting to the localhost:
- Open the terminal on your remote server machine
- Write
ssh localhostand press enter. - If you do not have an OpenSSH server installed then you will get a ‘Connection refused error’.
So if you do not have OpenSSH installed on your remote server then you can follow the below steps to install one.
- Open your terminal and run:
sudo apt update && apt install openssh-server - Type your password when prompted and then enter
Yto install. After a few minutes, the SSH server will be installed on your machine. - You can run this command to check the server status:
sudo systemctl status ssh - You will see an Active response on your window. This means you have successfully installed the SSH server and it is running well.
Now as you have installed an SSH server on a remote machine, you are ready to accept the connection request from a different remote device or your client device.
Installing an OpenSSH client
We need to install the OpenSSH client on our primary device which we will use to connect to a remote server or machine. So to check if you have already installed the OpenSSH client on your device or not. Follow the below steps:
- Open your SSH terminal.
- Type ssh and press Enter.
- If you already have a client installed, you will see an output like this:
sshusage: ssh [-1246AaCfGgKkMNnqsTtVvXxYy] [-b bind_address] [-c cipher_spec] [-D [bind_address:]port] [-E log_file] [-e escape_char] [-F configfile] [-I pkcs11] [-i identity_file] [-J [user@]host[:port]] [-L address] [-l login_name] [-m mac_spec] [-O ctl_cmd] [-o option] [-p port] [-Q query_option] [-R address] [-S ctl_path] [-W host:port] [-w local_tun[:remote_tun]] [user@]hostname [command]
Or if you do not have a client installed on your system then follow these steps to install one:
- Open your terminal and run this command:
sudo apt install openssh-client - Type your password when asked and hit enter. After a few minutes, the client will be installed on your device.
Now you can connect to any device which has an ssh server installed on it and you have a hostname and IP address of that device.
How to use SSH to connect to a remote server?
After installing OpenSSH on the client and server machines you can proceed to create a connection between them.
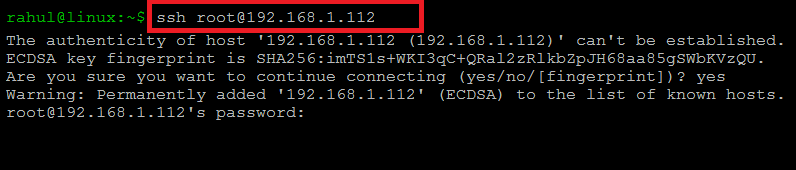
- Open a terminal on your client system and run
ssh your_username@host_ip_address. [host IP address is the, IP address of the device you are trying to connect with] If your username is as same as the username on the server machine then you can run this: ssh host_ip_address. - Next, type your password and click enter.
- If you are connecting to the server the first time and the remote server is not identified by your computer.
- After a few seconds, you will be connected to your remote server and you can perform your tasks.
- To exit the connection and return to your local device you can run this command exit.
So, you will get a warning message on your screen that you want to connect or not. Just type yes and click enter.
Here is the screenshot of ssh command:
Conclusion
SSH is the light, secured and easy method to connect to a remote server. Also, it is one of the most important things to be mastered by a System Administrator. It is a simple and common Linux activity and you can learn it for your daily use too.

1 Comment
Hello Rahul,
I installed Linux Machine on Vm. I want access ports in Linux machine from my host computer using NAT network. Can you let me know .