UDP, or User Datagram Protocol, is a fundamental component of the internet protocol suite that powers the global internet. It’s an alternative to TCP (Transmission Control Protocol) and offers a different strategy for the transmission of data packets between devices on a network. Understanding UDP requires an understanding of the choices network engineers and software developers make when they want to optimize network communication for different types of applications.
History of UDP
The User Datagram Protocol (UDP) is an older protocol, defined by John Postel in RFC 768 in August 1980. As the internet and digital technology have advanced, UDP has remained as a robust, efficient protocol that provides a foundation for many applications and higher-level protocols.
How Does UDP Work?
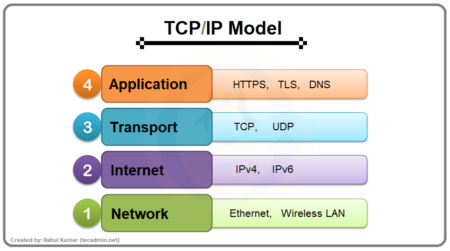
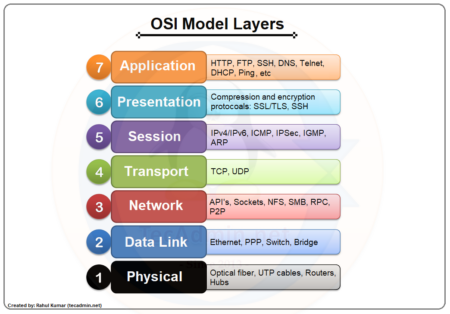
UDP operates at the transport layer of the TCP/IP protocol suite (or the OSI model’s fourth layer) and provides a minimalistic approach to message delivery. Unlike TCP, UDP is connectionless, meaning it doesn’t need to establish a persistent network connection between the sender and receiver before transmitting data.
With UDP, data packets, called datagrams, are sent to the receiver as they become available, without first notifying the receiver or waiting for acknowledgment that the receiver is ready. This is known as “fire and forget” because the sender doesn’t track or manage delivery. It just sends the data and moves on.
This protocol’s key features are:
- Connectionless: Unlike TCP, UDP doesn’t establish a connection before sending data; it just sends the data without checking if the receiver is ready.
- No Error Recovery: UDP does not offer error recovery. If a packet is lost in transmission, it’s gone; the sender won’t know about it, and the receiver can’t ask for it to be sent again.
- No Congestion Control: UDP doesn’t adjust its transmission speed to accommodate network congestion, unlike TCP.
- No Ordering of Data: If data packets arrive at the destination in a different order from how they were sent, UDP will not reorder them.
- Datagram Oriented: UDP is suitable for the simple transmission of data packets (datagrams) where speed is preferred over reliability.
- Checksum for Error Checking: UDP uses a checksum for error checking in the header and data to ensure data integrity, but it does not correct the error.
UDP and Other Protocols
While UDP lacks the reliability features of TCP, it compensates for these shortcomings with its speed and efficiency. For applications that require real-time transmission and where occasional data loss is tolerable, UDP is the preferable choice.
Examples include VoIP (Voice over Internet Protocol) calls, where a lost packet might cause a momentary audio glitch that’s preferable to waiting for retransmission, which would cause a delay. Similarly, streaming media services and online multiplayer games often use UDP, valuing the reduction in latency and the real-time transmission of data over the reliability of data delivery.
What UDP is used for?
UDP, or User Datagram Protocol, is a communications protocol that offers a fast and lightweight method of data transmission, albeit without the guaranteed delivery of TCP. It’s particularly useful for applications where speed and efficiency are more important than ensuring every piece of data arrives in the correct order. UDP is used in several important network services and real-time applications, including:
- Domain Name System (DNS): DNS is a system for converting human-friendly website names (like www.example.com) into numeric IP addresses that the internet can understand. DNS requests typically use UDP because these requests are small and can be served quickly.
- Streaming Media: Many streaming services use UDP to deliver content, especially for live broadcasts or real-time events. In these scenarios, if a few packets are lost or arrive out of order, it won’t significantly affect the viewing experience, making UDP a preferable choice for speed.
- Voice Over IP (VoIP): VoIP services, such as Skype or Zoom, often use UDP. Again, the real-time nature of these services means that speed is more important than perfect data delivery. A few lost packets in a VoIP call might result in a momentary drop in call quality, but this is generally preferable to the delay that would be caused by TCP’s need to acknowledge and retransmit lost packets.
- Online Gaming: Online multiplayer games require real-time interaction and quick responses. They often use UDP to reduce latency and lag, valuing the speed and efficiency that UDP provides over the reliability of TCP.
- Simple Network Management Protocol (SNMP): SNMP is a protocol used for managing devices on IP networks, and it operates over UDP.
- Trivial File Transfer Protocol (TFTP): TFTP is a simple, lock-step FTP that allows a client to get a file from or put a file onto a remote host. It’s used where user authentication and directory visibility are not required.
- Network Time Protocol (NTP): NTP is used to synchronize the clocks of computers over a network. It uses UDP because timing is crucial and packet loss can be tolerated.
- Video Conferencing: Like VoIP, video conferencing tools often use UDP to minimize delay and support real-time transmission.
Overall, UDP is a valuable protocol for applications where fast, efficient transmission is desirable and where it’s acceptable for some data packets to be lost or to arrive out of order.
UDP in Everyday Use
Despite its simplicity, or perhaps because of it, UDP plays a crucial role in the operation of the internet. For instance, the Domain Name System (DNS) uses UDP. When you type a web address into your browser, a DNS query is initiated to translate that web-friendly name (like www.example.com) into an IP address that the internet can understand, and this query is typically sent using UDP.
In conclusion, while TCP is a reliable and widely used protocol, the efficiency and speed of UDP make it the protocol of choice for many real-time applications. As with so many aspects of technology, the choice between TCP and UDP isn’t about which is best; it’s about which is best for a given situation. Understanding the strengths and limitations of both protocols allows network engineers and software developers to choose the right